Secure elements are specialized hardware components designed to safeguard sensitive data such as cryptographic keys, payment credentials, and identity information. They populate a vast array of digital devices ranging from mobile handsets to industrial control units — functioning as an impenetrable barrier to malicious software .
Their core mission stays unchanged , the structural design and deployment methods differ markedly depending on the use case , each suited for specific use cases and threat environments .
Recognizing the nuances between variants enables smarter decisions regarding protection levels and long-term viability.
The most common type is the embedded secure element , often integrated directly into a device's main processor or as a dedicated secure IC mounted on the PCB . These underpin nearly all major mobile payment platforms across iOS, Android, and other ecosystems, offering strong isolation between the operating system and sensitive operations . Their tight integration with the main CPU enables near-instantaneous processing of authentication requests , while maintaining a high level of tamper resistance . Yet, since they are permanently affixed to the board , they are not easily replaceable or upgradable after manufacturing , which restricts adaptability to evolving security standards .
An alternative model is the detachable secure element, routinely housed in programmable subscriber identity modules. These are designed to be physically inserted or swapped , enabling seamless provisioning for MVNOs and roaming services. They empower users to activate, deactivate, or update authentication tokens without hardware replacement. Permitting credential updates via cloud-based provisioning without physical intervention. Despite their usability, they risk compromise through brute-force removal or signal interception without adequate shielding, demanding enhanced cryptographic wrappers and attestation protocols for equivalent protection.
A third category comprises external secure elements , encompassing PKI tokens, smart card readers, and FIDO2 security keys. They are mandated in regulated industries for secure access and electronic signatures. Their portability enables cross-platform compatibility across PCs, servers, and workstations, granting administrators granular oversight of access events . They pose a threat when carried outside secured environments. Their transaction speeds are constrained by interface latency and protocol delays .
Emerging alternatives such as TEEs and HSMs , create hybrid models that mimic hardware-level isolation through software abstraction. Not classified as physical secure elements under industry definitions, they emulate similar functions using isolated processor zones and firmware-level controls . They reduce hardware dependencies and lower manufacturing overhead , they cannot match the silicon-level protection of isolated secure ICs .
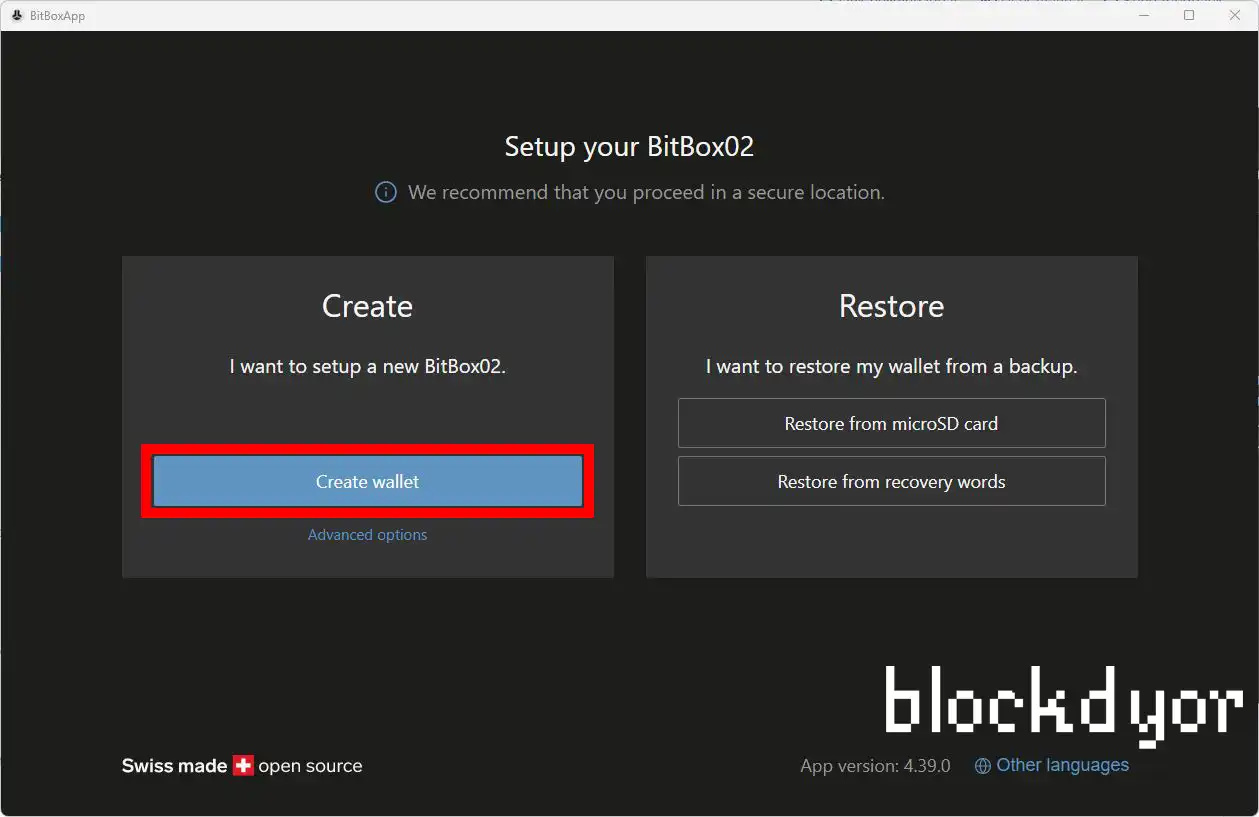
The optimal choice hinges on weighing protection level, usability, and budget constraints . For general-purpose devices, embedded chips deliver the strongest practical balance. For environments demanding dynamic credential management, removable or external forms are indispensable. Informed decisions demand insight into both the capabilities of the hardware and bitbox review the nature of the adversaries it faces.